Is Temp Mail Legal in 2026?
Yes — using temporary email is legal in most countries, including the United States, United Kingdom, and European Union, as there are no laws prohibiting the use of disposable or anonymous email addresses.
It is commonly used as a privacy tool to reduce spam and limit email exposure during online sign-ups.
However, its legality depends on how it is used, especially in cases involving abuse or fraud.
This makes temp mail a legal tool with usage-dependent boundaries.
This article explains how temp mail works legally, where the boundaries are, and when it can lead to restrictions or account blocks.
What Is Temp Mail?
Temporary email (temp mail) is a disposable email address that allows you to receive emails without using your personal inbox. It is typically used for short-term situations where users do not want to expose their primary email address.
Common use cases include one-time signups, receiving verification codes, and avoiding spam from websites or online services.
Unlike a permanent email account, temp mail is designed for temporary use and usually expires after a short period, meaning any messages stored in it may be lost permanently.
In simple terms, temp mail is a communication tool, not a long-term identity or account system.
Is Temp Mail Legal in 2026?
Yes — using temporary email (temp mail) is legal in most countries, including the United States, the United Kingdom, and the European Union.
This is because most cybercrime and fraud legislation frameworks focus on user behavior and intent rather than the communication tools themselves, meaning legality is determined by how a tool is used rather than the tool itself.
In legal terms, temp mail is treated as a neutral communication method. It becomes relevant only when it is used as part of unlawful activity.
What determines legality in practice
Temp mail is generally evaluated under three legal contexts:
- Lawful use: privacy protection, spam avoidance, anonymous sign-ups
- Abusive use: bypassing restrictions, fake identities, repeated fraud attempts
- Illegal use: phishing, identity theft, fraud, or deception
The key distinction is not the email itself, but the behavior attached to it
Temp mail is not regulated as a standalone service in most jurisdictions, but it is governed indirectly through general cybercrime and fraud laws. This is why it is widely considered legal, while still being restricted or blocked in practice by many platforms based on their own policies and risk controls.
The 3-Layer Model: Why Temp Mail Can Be Legal but Still Blocked
Whether temporary email is allowed or blocked depends on three independent systems that do not always align: legal rules, platform policies, and automated enforcement systems.
Understanding this separation is the key to resolving most confusion around temp mail.
1. Law (What is legally allowed)
At the legal level, using temporary email is generally not prohibited in most countries.
Law focuses on behavior, not tools.
Issues such as fraud, impersonation, or phishing may be illegal, but the use of temp mail itself is typically neutral.
In most cases: temp mail is legal unless used for illegal activity.
2. Terms of Service (What platforms allow)
Websites can set their own rules within the boundaries of applicable laws, even if those rules go beyond what is legally required.
Many platforms restrict:
- disposable email domains
- fake or non-permanent identities
- abuse of free trials or signups
So, even if something is legal, it may still be rejected or restricted by individual platforms because their usage policies are designed to control abuse, maintain security, and manage platform trust.
3. Enforcement Systems (What actually works in practice)
In real-world usage, decisions about temporary email are not based on legality or written platform rules, but on automated trust and risk evaluation systems.
These systems assess whether an email should be accepted by analyzing multiple signals, including domain reputation, abuse history, and behavioral patterns during signup.
In practice, this means platforms are not asking whether an email is “allowed” in theory. Instead, they are evaluating a single outcome:
Whether the signup appears trustworthy enough to process and activate.
As a result, even if temp mail is not explicitly prohibited, it may still be blocked, filtered, or silently rejected during registration or verification.
3.1 Underlying Security Infrastructure (Industry Implementation Layer)
These trust decisions are powered by widely used internet security and email infrastructure systems, which operate across millions of websites and services.
Key examples include:
- Spamhaus Domain Block List (DBL) — a global database used to identify and block known disposable or abusive email domains
- Google Postmaster Tools & Gmail reputation systems — used to evaluate domain trust based on email behavior and engagement signals
- Cloudflare Bot Management — a widely deployed security system that detects automated signups, abuse patterns, and suspicious traffic behavior
These systems operate at different layers of the internet infrastructure, from email delivery to web application security.
They are not designed specifically for temporary email services, but for general abuse prevention and trust scoring across the web.
Key Insight:Temp mail is not evaluated as a category.It is evaluated as a trust signal within global security systems that determine whether a request should be accepted, challenged, or blocked.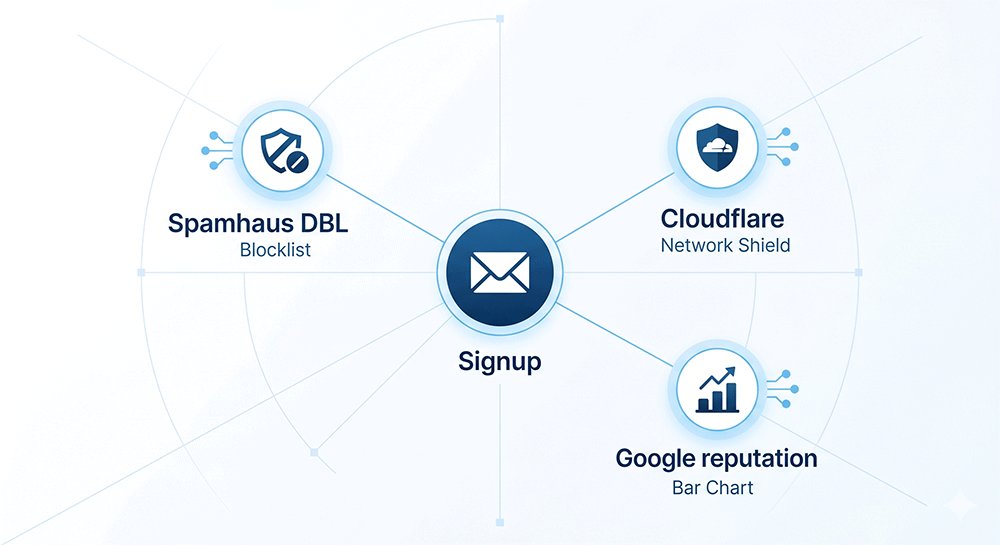
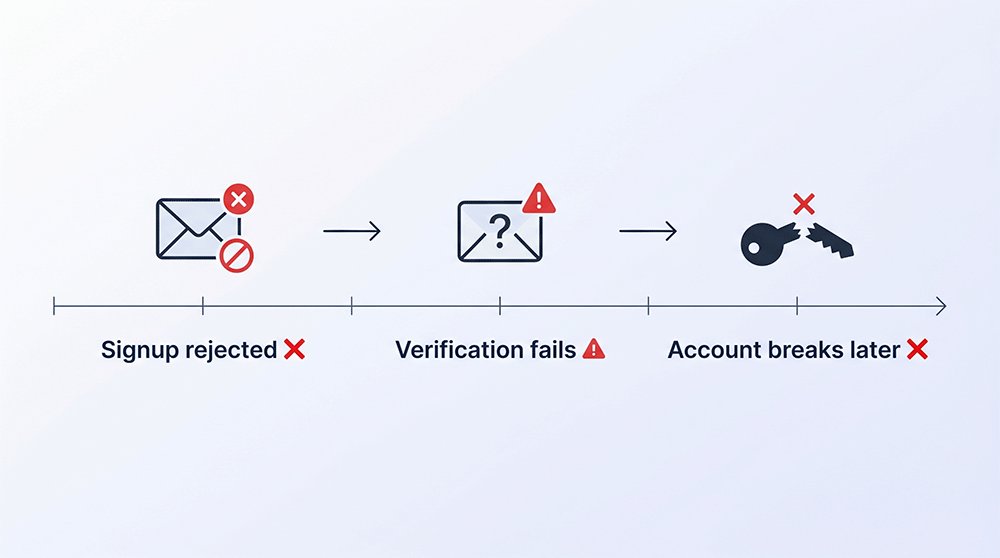
Why Temp Mail Fails in Practice
When temp mail does not work, it is usually not a technical delivery issue. Instead, failures occur because most websites rely on abuse prevention and email trust systems to filter disposable domains before or during account creation.
These systems are widely used across the internet, including infrastructure providers and anti-abuse networks such as Spamhaus DBL and Cloudflare security systems.
In practice, temp mail failures typically happen at three stages:
1. The email is rejected during signup
Many websites use domain filtering systems and disposable email blocklists, including databases like Spamhaus DBL (Domain Block List), to prevent known temporary email providers from being used during registration.
When a domain is flagged:
- the email is rejected before account creation
- the signup request may never reach the application backend
- the system may silently block the request without explanation
In practice, the signup is stopped before the account can exist.
2. The account is created, but verification fails
Some platforms allow signup but rely on email trust and delivery filtering systems to decide whether verification emails should be delivered.
In this stage, systems such as:
- Spam filtering and reputation scoring systems
- Cloudflare bot and abuse detection layers (used at the application edge)
- internal anti-fraud engines integrated with email providers
may block or delay verification emails sent to disposable domains.
As a result, the account exists but cannot be activated.
3. The account works initially, but breaks later
Even if temp mail passes initial checks, platforms often continue monitoring account behavior using risk-based security systems such as Cloudflare-protected abuse detection layers or internal fraud monitoring tools.
These systems may trigger:
- password reset restrictions
- login recovery failures
- forced re-verification requests
When the email expires, these recovery flows become unusable.
Temp mail failures are not random or caused by email delivery issues. They are the result of layered trust and abuse prevention systems used across modern web infrastructure.
These systems typically include:
- Spamhaus DBL → identifies disposable and abusive domains
- Cloudflare security systems → detect bot-like or abnormal signup behavior
- Email reputation frameworks → evaluate domain trustworthiness before delivery
In practice, these systems do not evaluate legality or intent.
They evaluate only one question:
“Is this email trustworthy enough to allow account creation and recovery?”
Can Websites Detect or Block Temp Mail?
Yes — many websites can detect and block temporary email (temp mail) services, and this is one of the most common reasons users experience sign-up or verification failures.
Most platforms do not block temp mail randomly. Instead, they use automated detection systems to identify disposable email domains and prevent them from being used during registration.
1. Domain Blacklist Detection (Most Common Method)
The most common method websites use is domain-based blocking.
Platforms maintain or integrate with disposable email databases (often called DEA or blocklists) that contain known temp mail domains.
If your email domain appears in these lists, the system may:
- reject the email instantly during sign-up
- prevent account creation
- trigger additional verification steps
In simple terms:
If the domain is known as “temporary,” it is often blocked automatically.
2. Domain Reputation Scoring
Beyond static blocklists, many platforms use domain reputation systems.
These systems evaluate how “trustworthy” a domain is based on:
- historical spam or abuse activity
- frequency of temporary registrations
- pattern of short-lived accounts
Domains with low reputation scores are more likely to:
- fail email verification
- be flagged as suspicious
- trigger CAPTCHA or manual review
This means even a valid temp mail address may still be rejected.
3. Behavioral & Technical Signals
Some platforms also analyze user behavior during sign-up.
Detection signals may include:
- repeated sign-ups from the same device or IP
- unusually fast form completion
- use of automation tools or scripts
- inconsistent browsing behavior
When combined with a disposable email domain, these signals increase the likelihood of blocking.
Summary
Websites can detect or block temp mail using multiple layers of protection:
| Method | What it does |
|---|---|
| Domain blocklists | Immediately reject known temp mail domains |
| Reputation scoring | Penalize low-trust email domains |
| Behavioral signals | Detect suspicious signup patterns |
This is why temp mail may work on one site but fail on another — detection is not universal.
Risks of Using Temp Mail
Temporary email is not inherently unsafe, but it can create serious limitations when used for accounts that require long-term access or trust.
Most risks are not immediate security threats, but practical consequences that appear over time.
1. Account recovery loss
The most important risk is losing access to accounts permanently.
Because temporary inboxes expire, any account linked to them may become impossible to recover.
This can lead to:
- lost password reset access
- permanent account lockout
- inability to verify identity later
This is the most critical long-term limitation of temp mail.
2. Inbox and message exposure risk
Some temp mail services use shared or publicly accessible inbox systems.
In such cases, incoming messages may be visible to others, including:
- verification codes
- login links
- password reset emails
Even in private systems, temp mail is not designed for long-term confidentiality.
The risk is limited in time, but high during active use.
3. Platform trust limitations
Many platforms treat disposable emails as low-trust signals.
This can result in:
- failed sign-ups
- repeated CAPTCHA verification
- reduced account trust or restrictions
These are system-level limitations, not legal issues.
The real risk is not using temp mail itself, but relying on it for accounts that matter long-term.
When Is It Safe to Use Temp Mail?
Temporary email (temp mail) is safe in specific low-risk situations, but it should not be used for accounts that require long-term access or recovery.
The key factor is simple: whether the account matters after initial use.
Safe Use Cases (Low-Risk Situations)
Temp mail is generally safe when it is used for short-term or disposable activities where future access is not required.
Typical examples include:
- one-time downloads (PDFs, guides, resources)
- promotional codes or limited-time offers
- testing apps, tools, or online services
- accessing content without account dependency
Key idea:
If nothing is lost after the session, temp mail is appropriate.
Unsafe Use Cases (High-Risk Situations)
Temp mail should be avoided when the account is tied to identity, money, or long-term usage.
Do NOT use it for:
- banking or financial services
- cryptocurrency wallets or exchanges
- work or business accounts
- e-commerce or subscription accounts
- any service requiring password recovery or identity verification
Key idea:
If recovery matters later, temp mail becomes a liability.
Decision Rule (Quick Check)
If you are unsure, use this simple rule:
Will I need this account again in the future?
Yes → do NOT use temp mail
No → temp mail is safe to use
This is the most reliable decision shortcut.
If you still want the convenience of temporary email but with better stability and longer retention, you can also consider using a more persistent temporary email service such as TempEmail.cc, which is designed for longer access and reduced risk of losing important messages.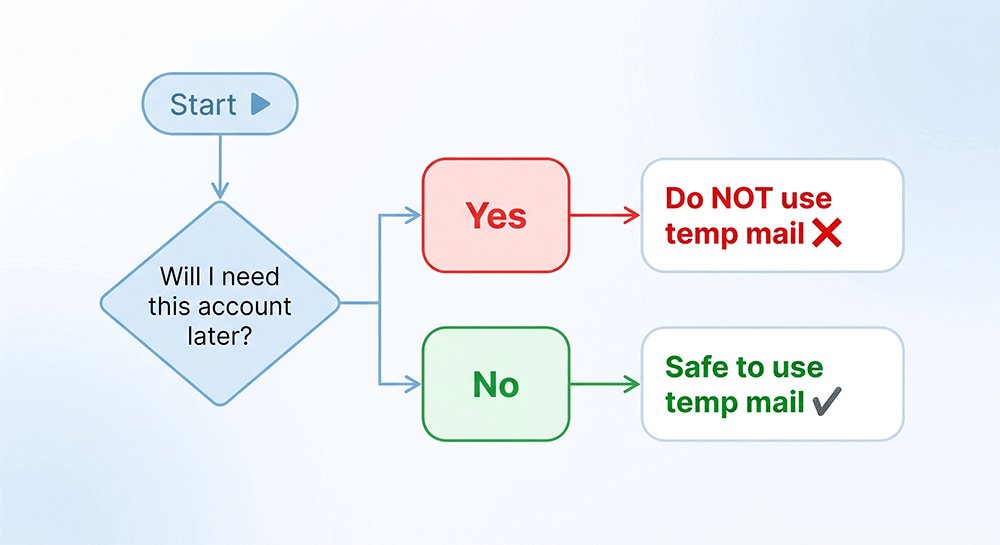
Summary
Temp mail safety depends entirely on how it is used.
It is generally safe for short-term, low-risk activities where account recovery is not needed, such as one-time sign-ups or testing services.
However, it should not be used for any accounts tied to identity, money, or long-term access, since temporary email addresses can expire and make recovery impossible.
In practice, temp mail should be treated as a temporary access tool rather than a permanent identity system.
Best Practices for Using Temp Mail Safely
Temporary email (temp mail) is safe when used correctly, but most problems happen due to misuse or unrealistic expectations. Following a few simple best practices can help you reduce risks and avoid common issues like account loss or verification failures.
1. Use Temp Mail Only for Low-Risk Activities
The most important rule is to only use temp mail for situations where losing access will not matter.
Good use cases include:
- one-time downloads or registrations
- testing websites or apps
- receiving verification codes for temporary access
- avoiding marketing spam from unknown websites
If the account is not important long-term, temp mail is appropriate.
2. Avoid Using It for Critical Accounts
Do not use temp mail for accounts that require recovery or long-term access.
This includes:
- banking and financial platforms
- crypto exchanges or wallets
- work-related or business accounts
- e-commerce accounts you plan to reuse
- any service tied to identity verification
Once the inbox expires, recovery becomes impossible.
3. Understand Platform Detection Limits
Many websites actively detect disposable email domains and may block or limit them. Even if temp mail works once, it may not work consistently across all platforms.
To reduce issues:
- avoid rapid or repeated sign-ups
- do not create multiple accounts in a short time
- expect some platforms to reject disposable domains entirely
This is normal platform behavior, not a technical error.
4. Treat Every Temp Email as Disposable
One of the most important mindset shifts is to treat temp mail as non-recoverable by design.
This means:
- do not store important data in accounts created with temp mail
- do not rely on it for password recovery
- assume the inbox will eventually expire or disappear
If you treat it as temporary from the start, most risks are avoided.
Summary
Safe use of temporary email is less about technical knowledge and more about adopting the right usage behavior. In practice, it works best when it is treated strictly as a short-term tool for low-risk tasks, while avoiding any critical services that require recovery or long-term access.
It is also important to understand that many limitations come from platform-level detection systems, which can block or restrict disposable emails regardless of how they are used. For this reason, users should always assume that temp mail is temporary by design and may not be reliable for future access.
Ultimately, the safest approach is simple: use temp mail for convenience, not commitment.
FAQ: Is Temp Mail Legal and Safe in 2026?
This section answers the most common practical questions about using temporary email services.
What happens if I use temp mail on important websites?
Using temp mail on important websites often leads to long-term access problems. Many platforms require email verification for password recovery, security alerts, or identity checks. If the temporary inbox expires, you may permanently lose access to the account. Even if the account works initially, future login or recovery requests can fail. For this reason, temp mail should only be used for low-risk, non-essential services where account recovery is not needed.
Why do some websites completely reject temp mail?
Many websites actively block temporary email domains using disposable email blocklists and reputation systems. These systems flag domains that are commonly associated with spam, abuse, or short-lived accounts. As a result, signup forms may reject the email instantly before account creation. In more strict systems, even newer temp mail domains are blocked based on behavior patterns, making it difficult to register regardless of the specific service used.
Can I recover an account created with temp mail?
In most cases, no. Accounts created with temp mail are extremely difficult to recover once the email inbox expires. Since password resets and verification links are sent to the original email address, losing access to that inbox means losing the recovery path. Some platforms may offer alternative recovery methods, but most rely heavily on email verification, making permanent recovery unlikely.
Is temp mail safe for receiving verification codes?
Temp mail can be safe for receiving verification codes in low-risk situations, such as testing services or temporary signups. However, it is not recommended for accounts that involve sensitive data or long-term use. Some temp mail services use shared inboxes, which may expose verification codes to others. Even in private systems, expiration time can cause codes to become inaccessible before use.
Why are verification emails not delivered to temp mail?
This usually happens due to platform-side filtering rather than delivery failure. Many websites block disposable domains before sending emails, meaning the message is never actually delivered. In other cases, the inbox may expire quickly, or the service may filter out known temporary providers. It is not an email delivery issue, but a combination of blocking rules and limited inbox lifespan.
Does using temp mail affect my account reputation?
Yes, indirectly. Many platforms use risk scoring systems that evaluate email domain quality, signup behavior, and device signals. If a disposable email is detected, the account may be assigned a lower trust score. This can lead to extra CAPTCHA checks, limited features, or stricter verification requirements. It does not affect your legal status, but it can impact platform experience and usability.
What is the safest way to use temp mail in daily life?
The safest way to use temp mail is to treat it strictly as a short-term tool. It should only be used for situations where losing access has no consequences, such as downloads, testing tools, or temporary registrations. It should never be used for financial accounts, work systems, or any service requiring recovery. The key principle is simple: if you may need the account later, do not use temp mail.
Can temp mail be used for free trials safely?
Technically it can be used for free trials, but many platforms explicitly prohibit it in their terms of service. Some services detect disposable domains and block signups immediately, while others may allow access but later suspend accounts if abuse is detected. Even if it works initially, you may lose access to trial benefits or related accounts. It is better used only where trial terms do not restrict email type.
Why does temp mail work on some sites but not others?
Many websites use different levels of email filtering systems. Some only rely on basic domain blocklists like Spamhaus DBL, while others use advanced reputation and behavioral systems such as Cloudflare or internal fraud detection engines. This means temp mail may work on low-security platforms but fail on services with stricter trust requirements.
Are all temporary email services treated the same?
No. Different temp mail providers use different domains, infrastructure, and reputation histories. Some domains are widely recognized and heavily filtered, while others have lower detection rates. However, most major platforms continuously update their blocklists, so success is never guaranteed.
Conclusion: Is Temp Mail Worth Using in 2026?
In 2026, temporary email remains a legal and practical tool for reducing online exposure and managing digital privacy.
When used correctly, it helps users limit unnecessary data sharing, avoid spam, and interact with websites without exposing their primary email address.
However, its value depends entirely on context. For short-term activities such as testing services, downloading resources, or accessing gated content, temp mail can be highly effective. For long-term accounts or services that require recovery and verification, it can create significant limitations.
Ultimately, temporary email is not a legality question but a trust and risk-management decision determined by how critical the account is.
Choosing the Right Temporary Email Approach
Not all temporary email services operate the same way. Differences in infrastructure, domain reputation, and inbox privacy can significantly impact reliability and usability.
Some services rely on heavily reused domains, which may be more likely to be blocked by websites. Others focus on maintaining cleaner domain infrastructure and more controlled usage environments, which can improve deliverability and reduce signup friction.
Understanding these differences can help users choose a solution that better fits their privacy needs without unnecessary disruption.